Today, almost all websites are delivered to the client via HTTPS, but HTTP is still frequently used for backend communication. To increase security Adobe has simplified the SSL configuration with AEM 6.3 and provides it as a feature called SSL By Default. This is intended to ensure that the internal connection to AEM instances is exclusively performed in an encrypted and authenticated way. This blog post describes a simple way to secure a local AEM instance using self-signed certificates for testing purposes.
Prerequisites
The following steps were evaluated on a Windows platform using cmd. It should be possible to perform them in the same way on another environment, but there may be small differences in the syntax of some commands. First, ensure that the tools below are installed:
Create self-signed certificate
AEM requires a private key/certificate pair in DER format for SSL setup. It can be created using the OpenSSL command-line tool.
1. Generate a private key of length 4096 bits.
openssl genrsa -out localhostprivate.key 4096
2. Create the certificate request with common name localhost from the private key.
openssl req -sha256 -new -key localhostprivate.key -out localhost.csr -subj "/CN=localhost"
3. Generate the SSL certificate and sign it with the private key (this is why it is called self-signed certificate). The certificate will be valid for one year.
openssl x509 -req -days 365 -in localhost.csr -signkey localhostprivate.key -out localhost.crt
4. Convert the private key to DER format.
openssl pkcs8 -topk8 -inform PEM -outform DER -in localhostprivate.key -out localhostprivate.der -nocrypt
Install SSL configuration via curl
Execute the following command from the directory where the private key/certificate was created.
curl -u admin:admin -F "keystorePassword=password" -F "keystorePasswordConfirm=password" -F "truststorePassword=password" -F "truststorePasswordConfirm=password" -F "privatekeyFile=@localhostprivate.der" -F "certificateFile=@localhost.crt" -F "httpsHostname=localhost" -F "httpsPort=8443" http://localhost:4502/libs/granite/security/post/sslSetup.html
Here AEM runs on port 4502 with credentials admin:admin. HTTPS is set up on port 8443. The keystore/truststore password has been set to password (Use a stronger secret in production).
If the command was successful you will get the following response:
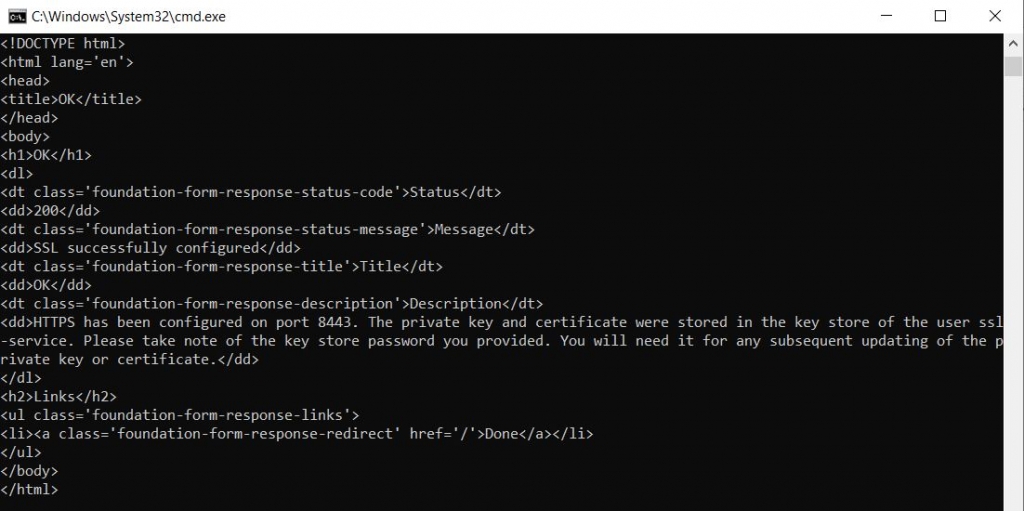
Now you should be able to open access the AEM instance on port 8443 over HTTPS: https://localhost:8443/
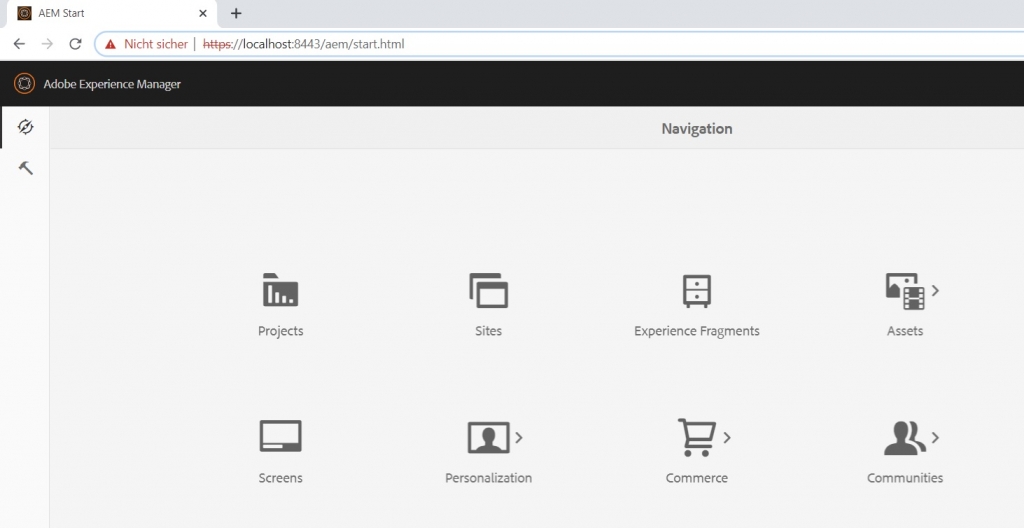
Note that the browser will most likely show a “Not Secure” warning because self-signed certificates are not trusted by default.
Disable HTTP
Currently, the AEM instance is still accessible via http://localhost:4502. In AEM 6.5 there is no option to deactivate HTTP by configuration. Be careful: The OSGi configuration Apache Felix Jetty Based Http Service contains a checkbox to disable HTTP. It has been deprecated but is still active. You may not be able to access your instance anymore if you change something on this dialogue. The new SSL configuration options can be found on Adobe Granite SSL Connector Factory.
Adobe proposes a different approach to deactivate HTTP. A sling mapping can be added to redirect incoming HTTP requests to the HTTPS port. Open CRX DE https://localhost:8443/crx/de/index.jsp and create a new node below /etc/map/http:
- Name: localhost.4502
- Type: sling:Mapping
Then add a new property to this node:
- Name: sling:redirect
- Type: String
- Value: https://localhost:8443
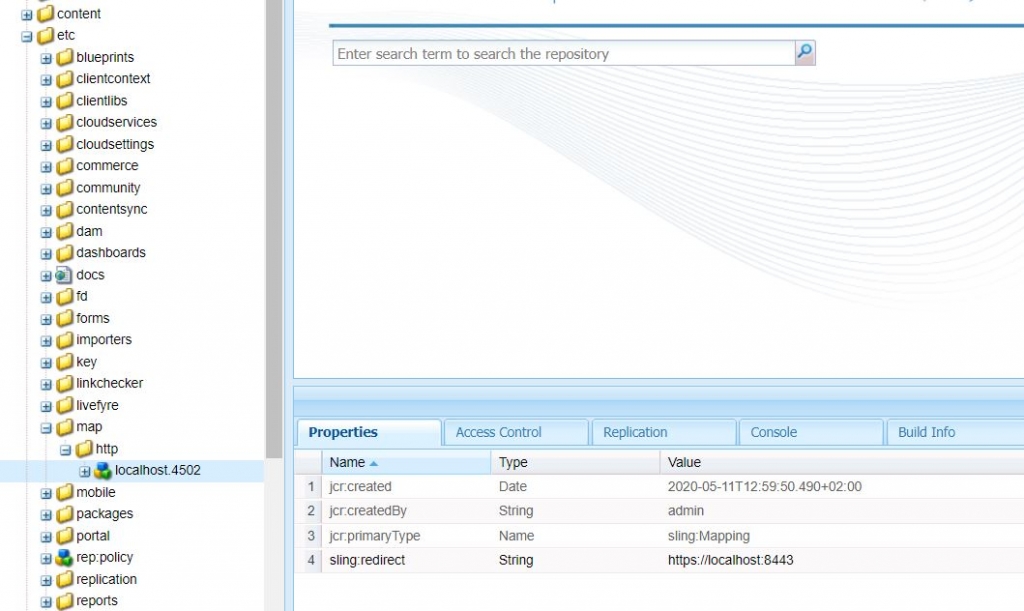
Click on Save All. Try to open http://localhost:4502 on the browser. You should now be redirected to https://localhost:8443/.
Conclusion
With the feature, SSL By Default Adobe provided a fast and easy way to set up SSL on an AEM instance. Self-signed certificates can be used for testing purposes on local/test instances. However, many organizations use their own PKI which manages the certificates. In this case, you should avoid self-signed certificates and use certificates signed by the certification authority of your organization.