In my last blogpost describing our way to the ISO 27001 certification we briefly mentioned one of our main goals to achieve with regards to obtaining and especially maintaining the certificate:
Automate the access controls
In today’s blog post, we’re diving deeper into how we achieved continuous monitoring and validation of access rights in our internal systems.
Understanding the challenges
Our experiences in the industry hinted us into the direction of the main challenges many companies are facing with regards to controlling access to systems and resources:
- Maintain an overview of authorized permissions spread over all the various systems and resources
- Track internal changes e.g. project assignments or reorganizations
- Give employees the right set of permissions for their job/role
- Maintain an overview of given permissions within those systems and resources
- Continuously monitor both sides and alert in case of any discrepencies
Companies that don’t manage to control either of those challenges are subject to vulnerabilities/problems such as privilege sprawl, inefficient (project/company) on- and offboarding and massive manual overhead for tracking everything spread across the landscape.
Our landscape-specific challenges
When we started working on our Access Control System the permissions were not centralized. They solely lived in:
- Our identity provider
- Our cloud provider
- Our cloud file storage system
- Our HRMS
Each system had its own way of handling permissions, roles and scopes. Permissions were regulaly evaluated, but we lacked a centralized overview. Thus, every access review turned into a manual investigation.
As with our other regular tasks, our goal was to leverage our ISMS and our automation skills so that we wouldn’t have extract and compare information manually.
Using our HRMS for managing Project Assignments and Roles
Our powerful HRMS Hello Today gave us a convenient entry point to managing the various project assignments and the roles within our projects. This gave us the following information out of the box:
- Who is working on which project
- What is their specific role in the project
- When does the project assignment start and end
With this information, we were able to create and maintain dynamic group assignments in our identity provider and integrate those into our IAM system without any additional overhead.
Order and provision Permissions
Every permission given in any system needs to be ordered and validated in our IAM. Using standard connectors and the information from our HRMS, we could provide a convenient ordering process for the project leads:
- Select the project
- Select the subject (preferably group or Service Account, in rare cases personal accounts)
- Select system and resource
- Select the permission(s)
Once the permission was ordered and (if necessary) validated, the IAM automatically provisioned the permission in the respective system.
Continuous validation
Per annex A.5.18 of the ISO 27001:2022 certification, we are required to regularly check the access rights given in all of our systems. As mentioned above, we didn’t want to rely on manual processes for repetitive tasks such as the access right validation, so we automated the whole process. Another benefit of this is that we are able to pretty much constantly run the access controls as necessary without any personal overhead.
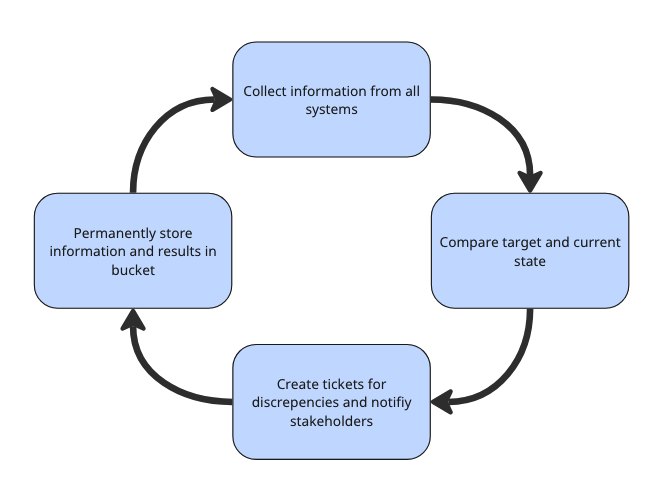
This process is triggered a) by (manual or automated) change of permissions in any of our systems and b) by a time-specific trigger. This allows us to always ensure that the current and the target state of permissions within our systems are as defined by our IAM. It also ensures that we don’t miss changes that were added and reverted between two time-specific runs.
Found discrepencies are created as a Jira ticket and afterwards synchronized to Drata, which in turn triggers a custom connection validation that gets directly reflected in our Drata dashboard.
All initial information (this includes orders, project assignments, system permissions, etc.) as well as any intermediate results (composed project information) and final results (discrepencies, open tickets) are permanently and immutably stored in a secure bucket which could be used in forensic analysis in the case of irregularities.
Revalidating the permissions
Another part of annex A.5.18 of the ISO 27001:2022 certification is that we have to regularly revalidate whether the permissions given still adhere to the “Need-to-know-” and “Least privilege-“concepts. This process is triggered automatically on a quarterly basis and creates according tasks for the resource owners.
Ready to Automate Your Access Controls?
Managing access rights across multiple systems doesn’t have to be a manual nightmare. Our approach to automated access control has not only streamlined our operations but also strengthened our security posture and helped us achieve ISO 27001 certification.
If your organization is struggling with access management, privilege sprawl, or the burden of manual compliance checks, we’d love to help. Whether you’re just starting your security journey or looking to optimize your existing IAM infrastructure, our team has the expertise to guide you through it.
Get in touch with us today to discuss how we can help you build a scalable, automated access control system tailored to your landscape. Let’s turn access management from a compliance burden into a competitive advantage.
Read more about Security @ N47.